by Alan Webber, Jeremiah Owyang, Altimeter Group Analysts.
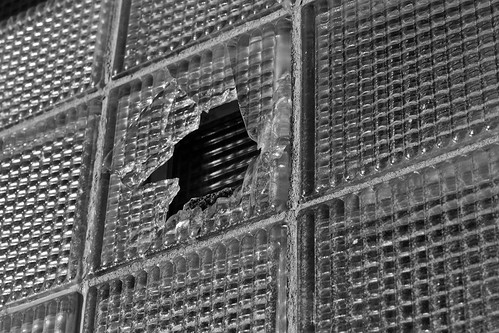
Yesterday’s Burger King brandjacking was an important reminder to brands and their agency and software partners about how vulnerable social media accounts are. These forms of attacks are increasing in frequency, such as Jeep’s recent twitter hack. Surprisingly, Altimeter Group’s research has found from analyzing 50 crises that 76% of crises could have been minimized or avoided had companies been prepared internally –external hacks are not the most common threats. While the press and media was quick to jump to conclusions that the Burger King account was “hacked” (with various daunting fingers pointing at McDonald’s and Anonymous) most threats come from inside –not external forces.
Multiple Points of Failure:
Below, we’ve compiled a list of potential points of failure, that all companies must prepare for. Anyone of these alone or combined could bring down the whole house of social cards.
- Management: Lack of password control. Burger King didn’t know who had access to the account or to the passwords. It is possible the same password was used across multiple accounts. Passwords need to be changed on a periodic basis.
- Breach: Organized hackers can comprise any system. An organized hacker can find multiple methods of intrusion including passwords, social engineering, software, or apps.
- Breach: Rogue employees or agency members (current or former). Without knowing who had access to the passwords, it is impossible to know if the account truly was hacked or if it was an a rogue employee, either current or former. Many social software systems are not tied to Active Directory or LDAP systems.
- Training and education: Lack of skills inside the organization. It isn’t clear that BK had the internal skills to actually manage the account, so they became dependent on an external firm. BK was highly dependent on an external agency to actually manage and control their twitter account.
- Software: Security of Social Media Management System Software. Though it isn’t clear, it is possible that the SMMS system employed by BK could have been hacked. This could have led to other failures in other social media systems.
- Software: Twitter and Facebook Apps. A number of apps on the Twitter and Facebook platform may have multiple forms of data access, which could yield information that could yield passwords, API access, or sensitive information.
- Software: Twitter and Social Networks susceptible. Twitter and Facebook themselves are targets from multiple intruders seeking to compromise systems. Recently, Twitter is under target from Chinese hackers as was Facebook, last week.
- Security: Network Intrusion. General network or firewall intrusion through online, network infiltration at corporate, mobile phone, agency, or even at Twitter corp.
Conclusion: Action Steps for All Brands and Agencies
Companies must analyze multiple points of failure and develop safeguards at each of the above listed steps. Start by sharing this checklist with internal legal risk and compliance teams, and operational social media teams, including agencies. Develop a process to test these at a regular basis and conduct social media fire drills with all constituents.
Additional Resources:
- Burger King spokesperson comments on agency and passwords Washington Post
- Sprinklr has provided a checklist for security
- Altimeter Report: Guarding the Gates
- Altimeter Report: Social Business Readiness
- Social Media Crises Simulation Vendors
- Alan Webber has cross-posted on his personal blog, and on Altimeter corporate blog.
Update: Minutes after posting this, Jeep was also hacked, and account is back to normal. Burger King and Jeep show brandly love.
Discussion: What other points of risk are not listed above? We’d love to hear your comments and additional points.
good insight
You’ve mentioned mobile phones which I think are quite pertinent to this topic. Myself and probably many other Community managers have Facebook Page Manager and Twitter apps installed on personal mobiles. If the mobile gets stolen (a frequent occurrence here in South Africa) then there is a security breach.
My solution so far to this issue is to make use of remote device management tools for my Android phones so I can wipe all user data from the phone in the case of theft or loss.